- Kraken user reportedly lost $18.2M through social engineering attack
- No platform breach—attack relied on manipulation and impersonation
- Human error remains the biggest vulnerability in crypto security
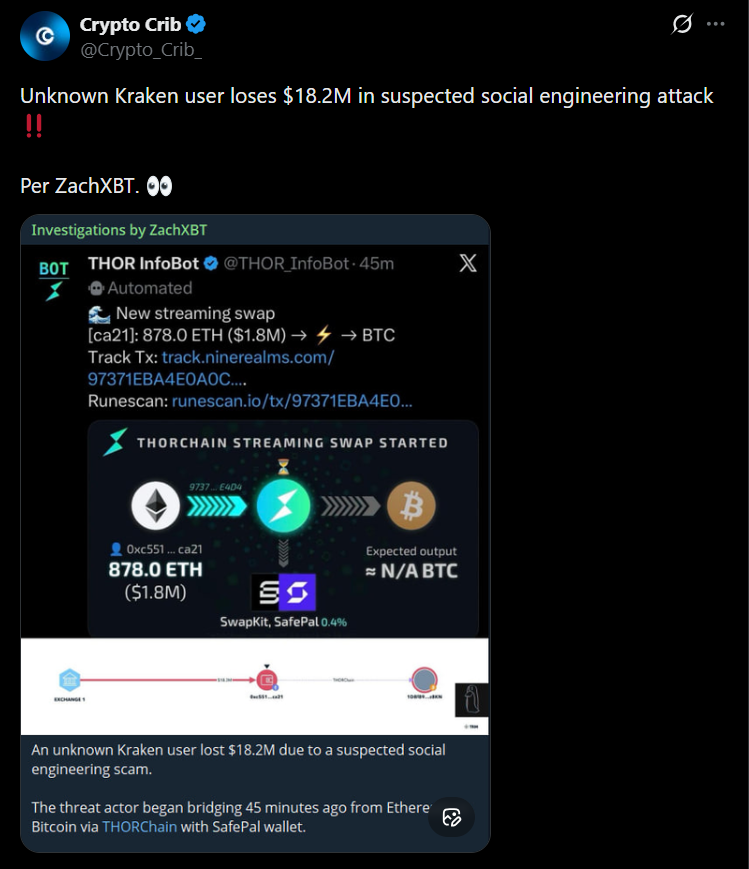
An $18 million crypto loss sounds like a system failure at first. But in this case, it wasn’t. According to on-chain investigator ZachXBT, the incident tied to a Kraken user appears to be another example of social engineering, not a hack of the platform itself.
That distinction matters more than it seems. The attacker didn’t break into Kraken’s infrastructure. Instead, they likely convinced the user to give access, approve transactions, or unknowingly compromise their own security. It’s a different kind of threat, and honestly, a more persistent one.
The Same Playbook Keeps Working
There’s a pattern to these attacks, and it’s becoming almost predictable. Impersonation is usually the starting point, posing as support staff, security teams, or trusted contacts. Then comes urgency. Something’s wrong, act now, fix this immediately.
In that moment, people don’t double-check. They react. And that’s all attackers need. Once access is granted, funds are moved quickly, often split across wallets and routed through multiple chains. Recovery becomes nearly impossible within minutes.
No Code Exploit, Just Manipulation
What’s striking is how low-tech these attacks can be. No smart contract bug, no exchange vulnerability, no advanced exploit. Just social manipulation, done well enough to bypass common sense.
And in many cases, it works better than technical attacks. It’s faster, cheaper, and doesn’t require breaking hardened systems. You just need one person to trust the wrong message at the wrong time.
Platforms Can’t Fully Protect Users
Even well-secured platforms like Kraken can’t prevent this kind of loss entirely. They can protect infrastructure, enforce safeguards, and monitor suspicious activity, but they can’t stop users from willingly approving transactions or sharing access.
That’s the uncomfortable reality. Security in crypto isn’t just about code, it’s about behavior. And behavior is much harder to control.
Why These Attacks Are Increasing
Social engineering is growing because it scales. Attackers don’t need to find a vulnerability in the system, they just need to find a vulnerable moment. And with more users, more capital, and more noise in the ecosystem, those moments are easier to create.
The rise of impersonation scams, fake support channels, and phishing attempts shows how the focus has shifted. It’s no longer about breaking platforms, it’s about bypassing them entirely.
The Weakest Link Hasn’t Changed
If there’s a consistent theme across crypto security incidents, it’s this, the weakest point is still the user. No matter how advanced the technology becomes, a single compromised interaction can override everything else.
Until that changes, stories like this won’t disappear. They’ll evolve, get more convincing, maybe even harder to detect, but the core dynamic stays the same.
Disclaimer: BlockNews provides independent reporting on crypto, blockchain, and digital finance. All content is for informational purposes only and does not constitute financial advice. Readers should do their own research before making investment decisions. Some articles may use AI tools to assist in drafting, but every piece is reviewed and edited by our editorial team of experienced crypto writers and analysts before publication.

 2 hours ago
16
2 hours ago
16



 English (US) ·
English (US) ·