A cross-chain message forgery drained 116,500 restaked ether from KelpDAO on April 18, triggering what Cardano founder Charles Hoskinson called the largest DeFi exploit of the year and a contagion event that pulled billions in total value locked from the broader ecosystem within 48 hours.
Key Takeaways:
- An attacker exploited KelpDAO’s cross-chain bridge on April 18, stealing 116,500 restaked ETH worth roughly $292 million.
- The breach triggered more than $13 billion in DeFi TVL outflows within 48 hours, hitting Aave, Compound, Morpho, and at least 9 other protocols.
- Charles Hoskinson says Midnight’s zero-knowledge proofs and multi-party computation could prevent this class of attack from repeating.
Hoskinson Explains Why Cardano’s Non-Custodial Staking Sidesteps Restaking Risk
Charles Hoskinson, founder of Cardano and Ethereum co-founder, broke down the attack in a video published from Wyoming, walking viewers through a custom artificial intelligence (AI)-generated incident report website.
“The standard DeFi threat model assumes smart contract bugs are the dominant risk,” Hoskinson said. “That’s not true anymore.”
He added:
“Bridges can be very problematic. A one-of-one verifier is not good. Don’t do that. And then the problem is that if they steal the money, DeFi lending is the exit condition. So basically, you can deposit, you can lend, and when you get those tokens, you’re getting tokens unconnected to the theft, and the collateral is poisoned effectively.”
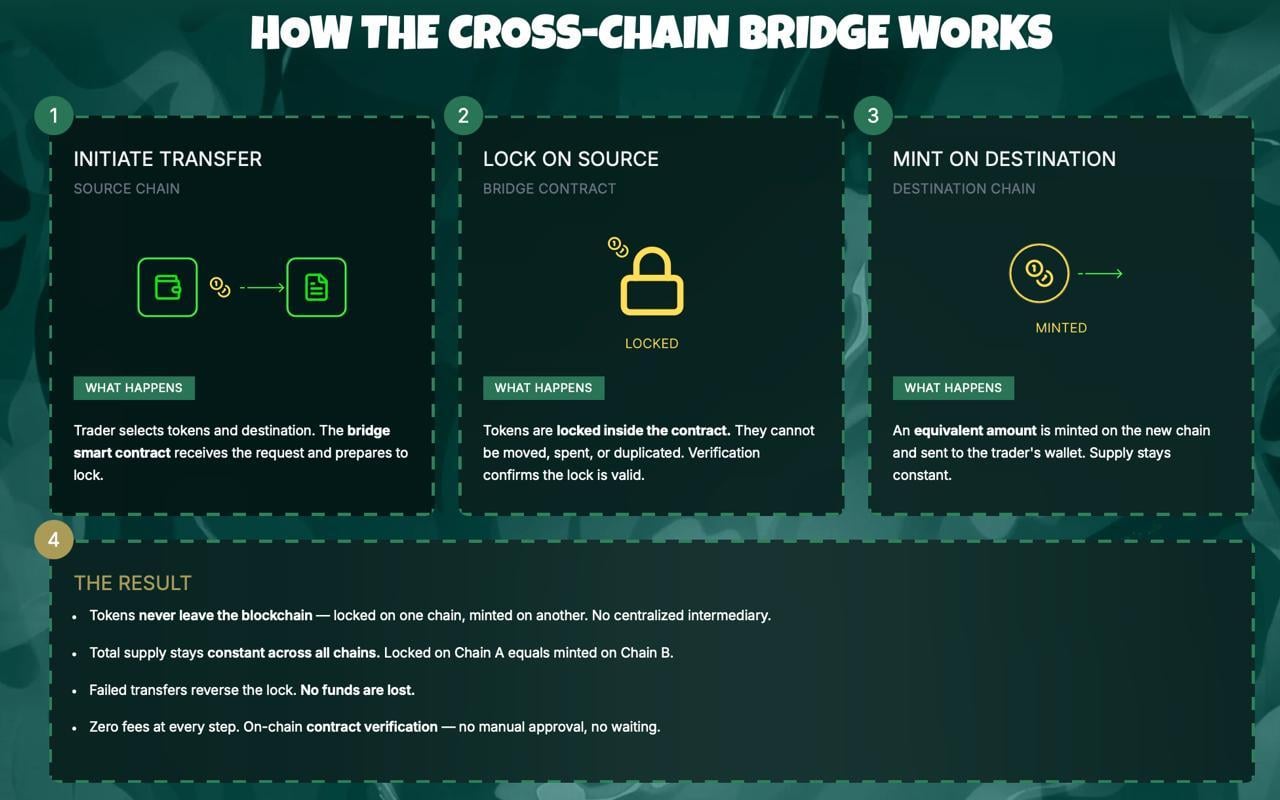
The attacker submitted a spoofed Layerzero message that reached the endpoint v2 contract connected to Kelp’s restake adapter, which then released the tokens from an Ethereum escrow. The forged packet claimed Uni-Chain endpoint ID 30320 as its source. Kelp’s cross-chain configuration relied on a single decentralized verifier network, a one-of-one setup that gave the attacker a single point to compromise.
The stolen tokens were not sold directly on decentralized exchange ( DEX) platforms, which would have crashed the price. The attacker deposited the restaked ETH as collateral in lending markets like Aave before Kelp or its partners could freeze positions, borrowing liquid wrapped ether against it and walking away with assets unconnected to the original theft. The poisoned collateral remained inside the borrowing markets.
Llamarisk’s joint incident report, published April 20, confirmed 83,471 ETH equivalent spread across seven attacker wallets on Ethereum core and Arbitrum. The report outlined two resolution scenarios. The first socializes a 15.12% haircut across all restaked ETH holders, producing roughly $123 million in bad debt absorbed by Ethereum core’s reserve. The second isolates losses at the layer two ( L2) level, repricing tokens to 26.46% backing and generating about $230 million in bad debt concentrated across Mantle, Arbitrum, and Base, while leaving Ethereum core untouched.
Aave alone saw between $6.6 billion and $8.45 billion in outflows. Wrapped ETH pools on Arbitrum, Base, Mantle, Linia, and Plasma hit near 100 percent utilization, effectively blocking withdrawals. At least nine DeFi protocols were classified as directly affected, including Compound, Morpho, Lido, Ethena, Pendle, Euler, Beefy, and Lombard Finance.
Three separate post-mortems have been published by KelpDAO, Layerzero, and Llamarisk. None agree on where responsibility sits. Layerzero announced April 20 that it would no longer sign or attest messages for any application running a one-of-one DVN configuration, pushing a protocol-wide migration to multi-verifier setups. Kelp maintains that Layerzero’s default configuration shipped with single-source verification across Ethereum, BNB Chain, Polygon, Arbitrum, and Optimism, and that allegedly 40% to 50% of all Layerzero OFT applications currently use the same one-of-one setup.
Onchain forensics suggest connections to the Lazarus Group, a state-sponsored hacking collective linked to North Korea. No independent forensics firm has issued a formal attribution, and the FBI has not commented publicly.
Hoskinson: ‘If You’re in Cardano Land, You Just Click Delegate … We’re Liquid Non-Custodial’
Hoskinson pointed to the attack as evidence that bridge verification failures have replaced smart contract bugs as the primary DeFi threat vector. He cited the $46-minute window between the initial drain and Kelp’s emergency pause as a sign that incident response matters but cannot outrun the speed at which stolen assets can be deployed into lending markets.
“What makes this novel is the contagion,” Hoskinson explained in his video. “It wasn’t just a bridge hack. It spread to lending, which then created bad debt contagion inside these lending protocols. It created a bank run, and we saw $13 billion of TVL pulled in a very short period of time for a $290 million hack. That’s a crisis of confidence.”
He framed Cardano‘s lower exposure as a function of its liquid, non-custodial staking design, which removes the need for the staking-to-liquid-staking-to- restaking wrapper chain that created the attack surface at Kelp. Hoskinson argued that Midnight, Cardano’s privacy-focused sidechain, addresses the core vulnerabilities involved.
Its Nightstream protocol folds entire chain states into proofs that travel alongside cross-chain messages, making forged messages verifiable before acceptance. “When people send messages, they can verify that what they’re seeing is correct,” he said. Multi-party computation support on Midnight would allow Layerzero to deploy turnkey two-of-three or five-of-seven DVN configurations with less operational friction.
Zero-knowledge proofs would block poisoned messages at the verification layer. Network anonymization would make the DDoS component of this class of attack harder to execute. He said AI tools, including frontier models reportedly accessible to the Lazarus Group through bribed insiders at major AI labs, are enabling attackers to scan entire codebases for emergent vulnerabilities that no single human reviewer would detect.
“Hacks are a part of life,” he said, “and they’re going to get much, much worse for everyone.”

 3 hours ago
19
3 hours ago
19





 English (US) ·
English (US) ·